Category Archives: events
RMU’s Data Science and Analytics Networking Event was a success!
RMU’s first Data Science and Analytics Networking Event, held on March 25, 2026, was a huge success! This event, organized by the Departments of Math and CIS, with the help of the Analytics Club, brought students face-to-face with data analytics and data science professionals, allowing them to learn about career options, skills needed in their field, problems they will face, and many other experiences. The event started with the introduction, where the panelists shared their bio, titles, and their job responsibilities, followed by the students’ questions. The second part included the roundtable, with networking and informal discussions between the students and the panelists. Overall, it was a great opportunity for our students to explore the job market and career expectations in their fields.

A big shout out to the panelists for taking their time to participate in the event:
· Caleb Armstrong, Business Analytics Associate III, MSA
· Koen Weichel, Assurance Associate, PwC
· Nicole Arvin, Senior Business Analytics Manager, MSA
· Dr. Mark Voortman, Chief Data Scientist, Liaison International, Othot Division
· Yinxiao Wang, Performance and Data Analytics Analyst, Allegheny County
· Dr. Ivan D’Souza, Lead Director, Technology Client Services in Digital, Data, Analytics, & Technology (DDAT), CVS Health
· Cullen Engle, Assurance Senior Associate, PwC
· Roger Kuo, Senior Director of Cloud Analytics, SAP
· Suchitra Suvarna, Senior Data Architect, SAP

2026 Upsilon Pi Epsilon (UPE) Honor Society Induction Ceremony
On April 12, 2026, we held the 2nd annual induction ceremony for the RMU chapter of Upsilon Pi Epsilon (UPE), the International Honor Society for the Computing and Information Disciplines. Congratulations to 27 inductees (undergraduate, graduate, and doctoral students) recognized for ranking in the top 30% of their class! This was a proud moment with faculty sponsor Dr. Karen Paullet, Department Head Dr. Jamie Pinchot, and student officers Kelson Bowman (President), Jesse Marks (Vice President) and Sean Miller (Secretary).

Joel Barnett from Howmet Aerospace to Present on April 14
Joel Barnett is a Cybersecurity Analyst at Howmet Aerospace, specializing in Data Loss Prevention and cyber investigations. He graduated from Penn State in 2023 with a degree in Security and Risk Analysis and is now pursuing a master’s degree at the University of Pittsburgh, focusing on Security and Intelligence Studies within the Graduate School of Public and International Affairs.
His current work centers on the evolving intersection of AI/ML and security across both the private and public sectors. In addition to his analyst role, he contributes to Howmet’s internship program and leads initiatives within the company’s cyber awareness efforts, helping develop the next generation of cybersecurity talent while strengthening organizational resilience.
He will be presenting on April 14th at 4:30 PM in Wheatley 110, covering:
- An introduction to his career path so far
- An overview of today’s IT and cybersecurity landscape
- Key cybersecurity career paths and how to prepare for them
- A live demo of any tool the audience wants to explore, including malware analysis, data loss prevention, ethics and compliance tools, email security, or network tools
- Open Q&A
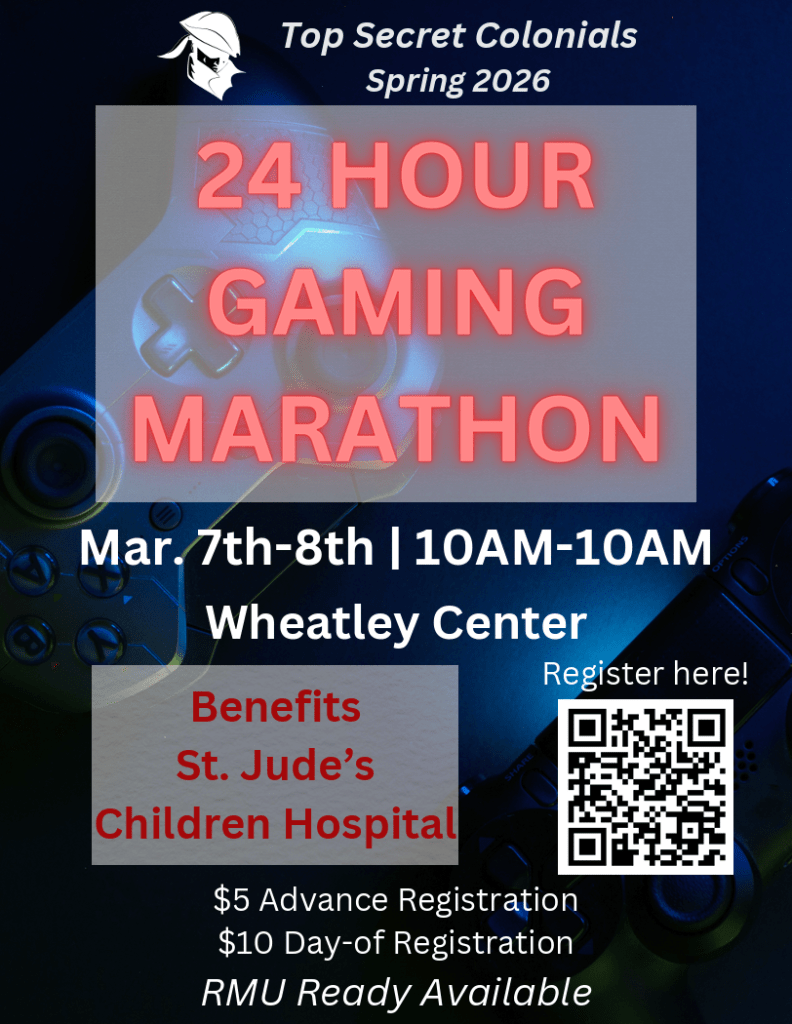
This presentation is sponsored by the Top Secret Colonials. RMU Ready credits will be awarded and pizza will be served. All students are welcome to attend!
NCFTA Cybersecurity Workshop

On February 4, 2026, twenty-one RMU students got to travel to the National Cyber Forensics and Training Alliance (NCFTA) headquarters in Pittsburgh for a cybersecurity workshop. Students got to hear a presentation from FBI Special Agent Aaron Hays, and a Chief Information Security Officer (CISO) panel featuring John O’Rourke from PPG and Dr. Jim Mahony from RMU. Dr. Jamie Pinchot accompanied the students for the trip and served as the panel moderator.
Students also had a chance to tour the facility, including the Malware Analysis lab and participate in a cybersecurity capture-the-flag exercise led by Emily Kerry, Intelligence Analyst (RMU ’24). Special thanks to Phill Miller, RMU CIO, for setting up this experience for the students. RMU hopes to make this an annual event.
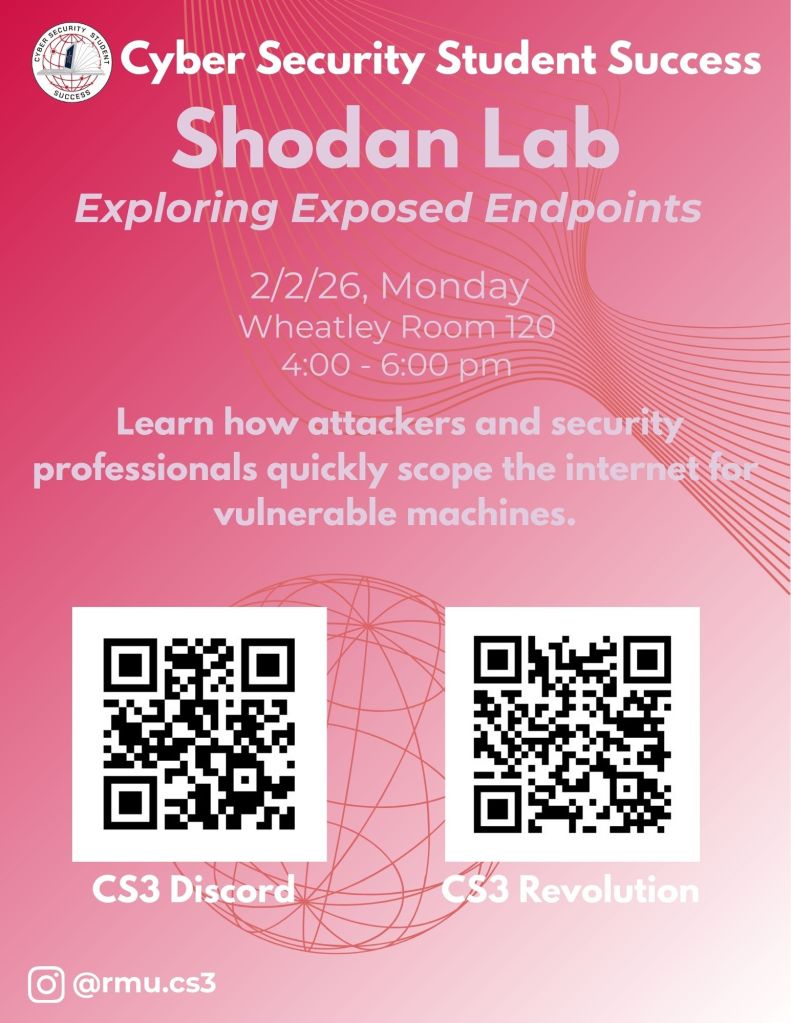
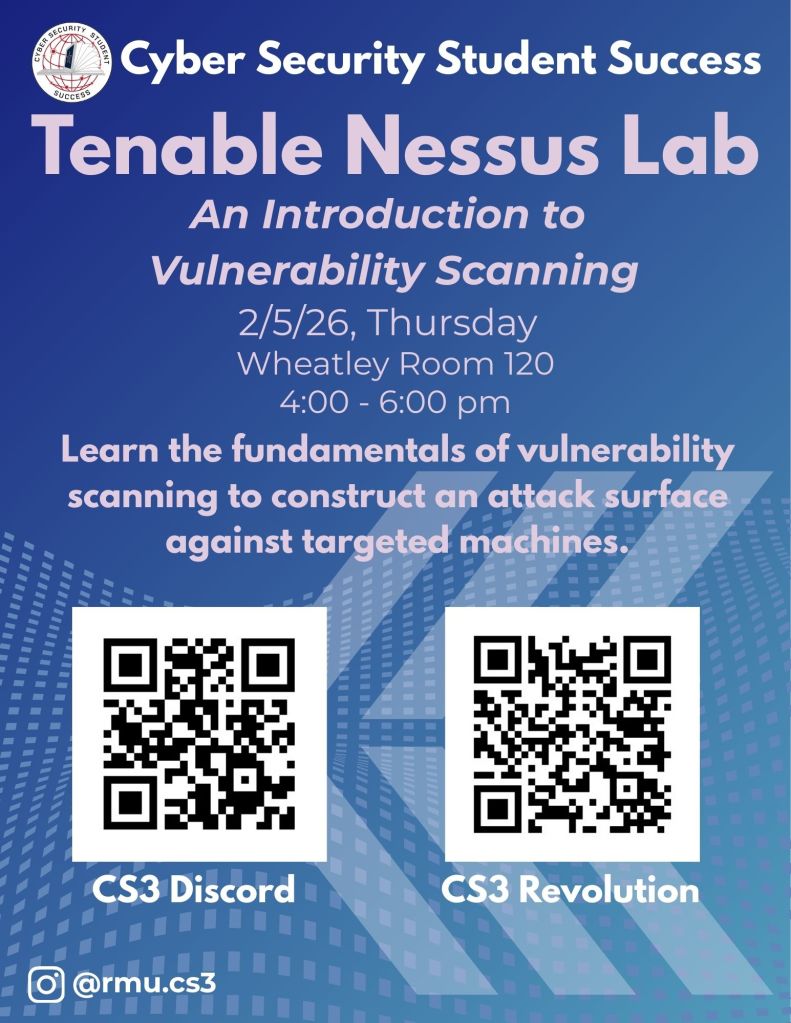
Cyber Security for Student Success (CS3) Club
Cyber Security for Student Success (CS3) has been established as a club at Robert Morris University. The purpose of the club is to create a community around peer-to-peer cybersecurity learning opportunities like workshops and competitions. The club is dedicated to empowering members through hands-on learning, professional development, and community outreach. CS3 meets every Monday and Thursday from 4:00pm – 6:00pm in Wheatley 120, so please stop by!
Join CS3 on February 2nd and February 5th from 4:00pm – 6:00pm for their first two labs: “Shodan – Exploiting Exposed Endpoints” and “Tenable Nessus – An Introduction to Vulnerability Scanning”.
Cyber Workshop for RMU @ National Cyber Forensics & Training Alliance (NCFTA)
The CIS Department has organized a workshop for RMU students at the National Cyber Forensics & Training Alliance (NCFTA) in Pittsburgh. The workshop will focus on areas of interest to cybersecurity students, but all computing students are welcome to attend. However, the event will be limited to the first 20 students. Transportation to/from the event and a light lunch will be provided by the CIS department.
Cyber Workshop for RMU @ National Cyber Forensics & Training Alliance (NCFTA)
Location: 2000 Technology Dr, Pittsburgh, PA 15219
Event Date: Wednesday, February 4th 2025
Event Time: 8:00 am – 2:00 pm
Agenda:
8:15 am Bus from Campus to NCFTA
9:00 am FBI Briefing on Current Events (unclassified) and Career Info
Aaron Hays, FBI Special Agent
9:45 am Industry CISO Panel
John O'Rourke, Chief Information Security Officer, PPG
Jim Mahony, Chief Information Security Officer, RMU
10:30 am Hands-On Cybersecurity Capture-the-Flag Exercise
11:30 am NCFTA Facility Tour including Malware Lab
12:00 am Lunch with:
Emily Kerry, Intelligence Analyst at NCFTA; RMU Class of 2024
1:00 pm Bus returns to Campus
Sign-up Below
If you are interested in attending this event, please fill out the application below and submit to indicate your interest.
Click here: Cyber Workshop Application
You will be notified in January if you have been selected to attend the event (limited to the first 20 students), and asked to confirm your attendance at that time. (If you have class on Wednesdays, you will need to miss class to attend this event on February 4th. You will have time to discuss with your professor(s) to ensure that this will be OK before confirming your attendance.)
2025 Three Rivers Info Security Symposium (TRISS) Conference
The Three Rivers Information Security Symposium (TRISS) is an annual, single-day event featuring multiple presentation tracks. It serves as a vital meeting ground for Pittsburgh’s leading IT and security professionals, enabling them to exchange knowledge and foster collaborative partnerships.
This symposium is an entirely volunteer-driven effort, dedicated to raising awareness, encouraging cooperation, and strengthening expertise within the regional information security sector.
TRISS is proudly sponsored and organized by a coalition of influential local organizations, such as:
- RMU’s Top Secret Colonials (TSC)
- Women in CyberSecurity (WiCyS)
- Information Systems Security Association (ISSA)
- Infragard Pittsburgh Members Alliance (IPMA)
- Information Systems Audit and Control Association (ISACA)
Furthermore, the symposium shows its commitment to the future of the field by offering a robust education and scholarship program.

The conference attracts key experts and executives from major Pittsburgh institutions, including U.S. Steel, PNC, PPG, Wesco, UPMC, and others. A commitment to quality is upheld through a merit-based speaker selection process, guaranteeing a diverse and unbiased program.
This year, 30 students from RMU were in attendance! The symposium provided them with a truly great learning and networking opportunity, allowing them to immerse themselves in the latest industry trends, cutting-edge research, and practical defense strategies presented by leading security professionals.
TRISS 2025 was a fantastic success, underscoring the vital connection between local industry groups and the next generation of cybersecurity talent. We look forward to seeing everyone again next year!
TSC Sponsored – Industry Presentation from Nerds to Go
Join Top Secret Colonials for a Special Industry Presentation on Wednesday, November 12th at 4:30, following the TSC meeting in the Wheatley Atrium.
Representatives from Nerds to Go, a division of True North, will be visiting campus to share insights into the technology driving their companies. Speakers include Zachary Prytash, Trey Trucksis, and CEO Chuck Bailey, who will discuss their work and the exciting innovations shaping their field.
They’ll also be actively recruiting for internship and full-time job opportunities, so this is a great chance to connect and explore potential career paths.
RMU Ready Points will be awarded to attending students. Pizza will be served.
Don’t miss this opportunity to learn and network.