Joel Barnett is a Cybersecurity Analyst at Howmet Aerospace, specializing in Data Loss Prevention and cyber investigations. He graduated from Penn State in 2023 with a degree in Security and Risk Analysis and is now pursuing a master’s degree at the University of Pittsburgh, focusing on Security and Intelligence Studies within the Graduate School of Public and International Affairs.
His current work centers on the evolving intersection of AI/ML and security across both the private and public sectors. In addition to his analyst role, he contributes to Howmet’s internship program and leads initiatives within the company’s cyber awareness efforts, helping develop the next generation of cybersecurity talent while strengthening organizational resilience.
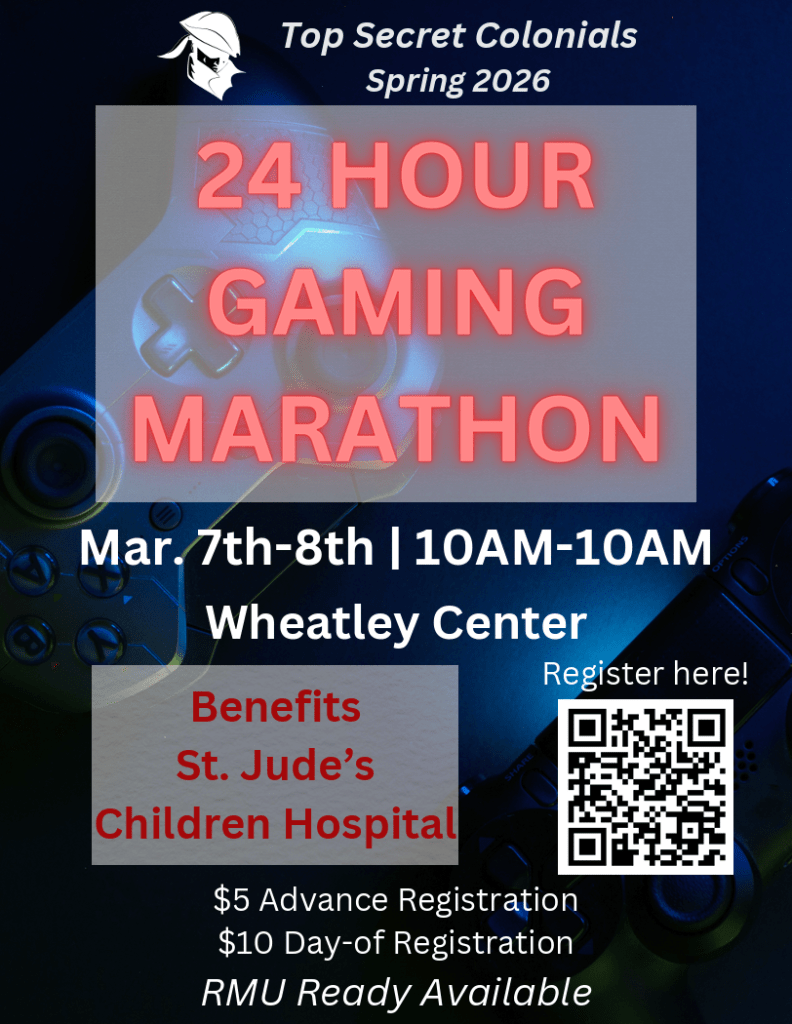
He will be presenting on April 14th at 4:30 PM in Wheatley 110, covering:
- An introduction to his career path so far
- An overview of today’s IT and cybersecurity landscape
- Key cybersecurity career paths and how to prepare for them
- A live demo of any tool the audience wants to explore, including malware analysis, data loss prevention, ethics and compliance tools, email security, or network tools
- Open Q&A
This presentation is sponsored by the Top Secret Colonials. RMU Ready credits will be awarded and pizza will be served. All students are welcome to attend!